CoreCLR Security Model
Mono is quickly approaching having a complete implementation of the CoreCLR security model for Mono. This is being developed primarily for use in Moonlight.
This new and simplified security model allows Moonlight to download and execute untrusted code and run it inside a sandbox. A full implementation requires Mono to have an executable image verifier (making sure the binary that we download follows all of the rules and does not try some funny business), an IL verifier that ensures that the code does not contain any unsafe operations and the sandbox system that ensures that the downloaded code only calls methods that it has permission to call.
Click for passable illustration of how the sandbox works.
MSDN has a short introduction to the sandbox and I blogged a long list of links to the original blog entries that documented it.
CoreCLR security can be customized using a handful of attributes. Instead of sprinkling our source code with the attributes and a gazillions #ifdefs we are using our Mono Linker and a few tools and configuration files to reshape our libraries to contain the necessary attributes required to secure the sandbox. We use a number of tools to automate this process and a manual auditing process to audit the results.
This is cool because this is a much simpler sandbox system than CAS ever was and our tools make it very simple for third parties embedding Mono into their applications to create their own sandboxes and reshape what is allowed or not allowed by the sandbox based on their specific needs.
The bad news: this sandbox is only available from trunk right now and will not be easily available until Mono 2.6.
Posted on 31 Mar 2009
Mono 2.4 and MonoDevelop 2.0 released
We just released two big projects we have been working on for quite a while.
Mono 2.4 is a much faster, scalable and tuned version of Mono, like you have never seen before. Major highlights from the previous release are documented in our release notes.
And MonoDevelop 2.0

And a brand new web site
I previously blogged about the list of all the new MonoDevelop 2.0 features. The most visible one is the integrated debugger both for Mono applications and for C-based applications (using GDB).
Dogfooding: In addition to all the nice features in MonoDevelop 2.0, Lluis migrated the web site for MonoDevelop from MediaWiki to the Mono-powered MindTouch Deki content management system.
Posted on 30 Mar 2009
Game Developers Conference
 I am heading out to the Game Developers
Conference in San Francisco as an attendee after some
strong endorsments from some friends on tweeter.
I am heading out to the Game Developers
Conference in San Francisco as an attendee after some
strong endorsments from some friends on tweeter.
If you are at the GDC or in San Francisco and would like to get together at some point drop me an email (miguel at gnome dot org). Or if there are any great hacker get-togethers for game developers, I would love to hang out with them.
I would not want to dissapoint, and as a one trick pony kind of person, I will likely be talking about Mono, Moonlight and the virtues of managed code to anyone willing to listen.
Looking forward to see what my friends have been up to. I can not wait to see the C# repl in a Unity/Web app.
Posted on 24 Mar 2009
Moonlight 1.9 and Ogg
As I mentioned on a previous post Silverlight 3 opens the doors for developers to plug their own Codecs into the Silverlight media pipeline.
Only a few hours later I read on twitter that Atsushi and Rolf has implemented not only the Ogg/Vorbis Codec for Silverlight 3, but also implemented the Silverlight 3 API in Moonlight:
This means that you can now use your Silverlight-based players to playback Ogg/Vorbis content. Theora and Dirac are still missing, but with the sample code that we now have, it is going to be merely a weekend hack to get it done. Fluendo has a nice implementation of both already in Java.
Update on May 6th, 2009: open source implementations of Dirac, Vorbis and adpcm now live in the mooncodecs module.
Update: link fixed.
You can see the sample in action in Atsushi's test page.
Like Jo said on IRC:
it also works on SL3 though. that's the bit that excites me, since it means we have proper cross-platform playback with Free codecs *today* working in most browsers that matter
In the words of Annie Hall: La de da.
Go Moonlight Go!
Posted on 24 Mar 2009
Hot Hot Hot: Silverlight 3 Pluggable Codec Architecture (OGG, Theora, Vorbis and Dirac).
Burried in the list of what is new in Silverlight 3 there is this gem:
Extensible media format support: With the new Raw AV pipeline, Silverlight can easily support a wide variety of third-party codecs. Audio and video can be decoded outside the runtime and rendered in Silverlight, extending format support beyond the native codecs.
What the above means is that with Silverlight 3 in addition to the built-in codecs for VC-1 and H.264 and the built-in containers (ASF and MOV) developers can plug an arbitrary audio or video codec and containers into the pipeline to support other formats like Dirac, vorbis, theora and the OGG container.
Both the codecs and the container parsers are authored using C# (or any other .NET supported language).
It would be nice to use Mono.SIMD where appropriate for these codecs. Mono.SIMD works out of the box on .NET, but it is hardware accelerated in Mono.
Atsushi at Novell has done some of the work to get an old C#-based Vorbis codec working with Silverlight 3. We will post more details when we have more information (the fix is on SVN).
Posted on 23 Mar 2009
Mono and the Google Summer of Code 2009
Once again, the Mono project will be participating in the fabulous Google Summer of Code.
This is a great opportunity for students that want to get involved with open source to contribute, learn and get paid for their work during the summer.
We have been very lucky in recruiting some great students in the past years and these students have taken on some very sophisticated tasks over the years. MonoTorrent, ParallelFX, FastCGI for mod_mono, WinForms designer and theming, Gendarme development, Gtk# widgets and much more.
We have posted some ideas for students to get started, but students that are passionate about Mono should feel free to pitch their own ideas.
We tend to pick students for advanced projects over the milder, simpler tasks.
This year, I am excited about a few special projects:
- Making the Mono VM use LLVM as a code generation backend.
- Porting Mono.SIMD to new architectures.
- ParallelFX updates.
- Using NVidia's VDPAU library to provide a new codec implementation in Moonlight to support VC-1/H.264.
- Managed (C#) implementations of Dirac and Vorbis as Silverlight 3 codecs.
- A Database designer Add-in for MonoDevelop to support DBML editing.
There are many more of course, but the above are the ones that are making me drool.
Posted on 23 Mar 2009
BareFTP
Christian just pointed me to BareFTP a graphical file transfer client that supports FTP, FTPS, SSH and SFTP protocols to transfer files.

I am a command line kind of person, but many of my friends like to use GUI clients for this.
Posted on 22 Mar 2009
Hot Off the Presses: Unity Goes to Windows
Unity has announced that their Unity 2.5 IDE is now cross platform and now works Windows in addition to MacOS.
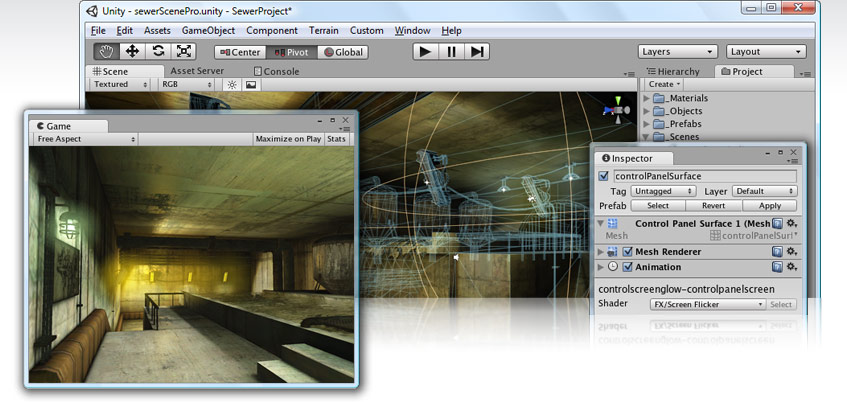
Unity rebuilt the entire Cocoa-based UI that they had previously with a Unity-powered UI. The entire UI is now built in C# using the Unity built-in APIs (all the controls, views, widgets).
This is a little bit like a compiler compiling itself. This time it is an IDE built using the IDE itself
Posted on 19 Mar 2009
Moonlight brings Playboy archives to Linux
Since yesterday's announcement that the Playboy archives would be hosted using Silverlight's DeepZoom folks have been hard at work getting the remaining Silverlight 2 features implemented in Moonlight.
Posted on 19 Mar 2009
Lucas integrates csharp REPL into Unity
Lucas Meijer has integrated Mono's C# REPL into Unity.
Visit his post and check out the flash demo of the C# REPL in action.
Posted on 18 Mar 2009
Mono and Qt
The KDE folks have created some brilliant bindings for Mono and .NET called Qyoto.
But there is nothing like a polished application to really test the bindings. This week Eric Butler announced Synapse: an advanced Instant Messaging platform.
This is the first large application built with Qt/Qyoto/Mono and it is a beautiful application:
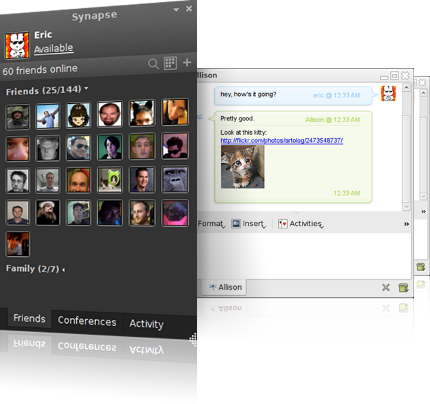
I had a chance to see Synapse live a couple of weeks ago in Seattle when we met Eric for dinner. Eric has written a very polished application. This is what love does to software.
Congratulations to Eric for the release of his app, to the Qymono crowd for creating these polished applications and Nokia/Trolltech for releasing Qt under the LGPL license.
Developers interested in doing Qyoto development with MonoDevelop can take advantage of the QyotoDevelop add-in that Eric created as well. This add-in generates code from the Qt Designers UI files (click for a screenshot).
Posted on 16 Mar 2009
Voices from Post-Saddam Iraq
My friend Victoria Fontan who works at the UN's University for Peace in Costa Rica just published the book from her research work on Iraq.
The book is Voices from Post-Saddam Iraq: Living with Terrorism, Insurgency, and New Forms of Tyranny. From the editorial reviews:
Even today, most Americans can not understand just why the fighting continues in Iraq, whether our nation should be involved there now, and how we could change our tactics to help establish a lasting peace in the face of what many fear will become a full-fledged civil war. In the book at hand, Victoria Fontan - a professor of peace and conflict studies who lived, worked and researched in Iraq - shares pointed insights into the emotions of Iraq's people, and specifically how democratization has in that country come to be associated with humiliation. Including interviews with common people in Iraq this work makes clear how laudable intentions do not always bring the desired result when it comes to international conflict and cross-cultural psychology. For example, Fontan explains, one might consider the comment of a young Shiite: "The greatest humiliation of all was to see foreigners topple Saddam, not because we loved him, but because we could not do it ourselves." This gripping text is focused on a new and growing area of human psychology - humiliation studies.
Please vote to have the book available on Kindle. I got a hardcopy, but I would love to travel with it instead.
Posted on 16 Mar 2009
Mono's Text Template Transformation Toolkit (T4)
At the ALT.NET Seattle conference I was introduced for the first time to the Text Template Transformation Toolkit. Also known as T4. T4 is built into Visual Studio and developers use TT to generate code from all kinds of data sources. This tutorial covers the basics.
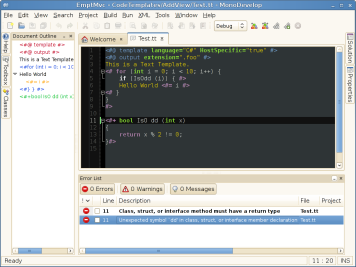
T4 Support in MonoDevelop, with error reporting and document outline.
T4 is very much like ASP.NET in that code is mixed with output code. Additionally TT has access to data on its "host". This allows for some creative data extraction from the environments before it generates output.
To my surprise T4 thing is wildly used by lots of people. Daniel Cazzulino's company has a product just to improve Visual Studio's support for editing .tt files.
What really got me interested in T4 were the templates that Damien wrote to convert from DBML files into C# code that is suitable for use with Linq. A nice replacement for the SQLMetal tool.
I mentioned this -in passing- to Michael Hutchinson as he had been working on ASP.NET MVC support for MonoDevelop and there are some nice ASP.NET MVC T4 files out there.
In a week he implemented: the T4 command line tool, the MonoDevelop host (to support ASP.NET MVC) and he even added syntax highlighting to it (see the above screenshot).
We have also started using it to migrate the code that previously used assorted WriteLines to generate RPM files from Visual Studio/MonoDevelop projects into a nice T4 template:
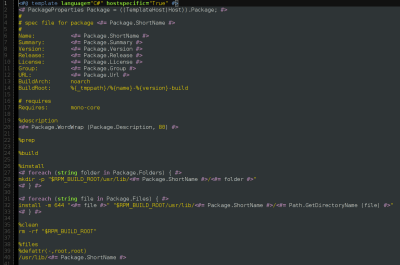
Packaging Template
Posted on 10 Mar 2009
Blog Search
Archive
- 2024
Apr - 2020
Mar Aug Sep - 2018
Jan Feb Apr May Dec - 2016
Jan Feb Jul Sep - 2014
Jan Apr May Jul Aug Sep Oct Nov Dec - 2012
Feb Mar Apr Aug Sep Oct Nov - 2010
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2008
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2006
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2004
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2002
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Dec
- 2022
Apr - 2019
Mar Apr - 2017
Jan Nov Dec - 2015
Jan Jul Aug Sep Oct Dec - 2013
Feb Mar Apr Jun Aug Oct - 2011
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2009
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2007
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2005
Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec - 2003
Jan Feb Mar Apr Jun Jul Aug Sep Oct Nov Dec - 2001
Apr May Jun Jul Aug Sep Oct Nov Dec